Security
Your Trust Is Our Pride
With a vast global presence, our list of clientele includes some major players identifying themselves in the BFSI, Retail and E-Commerce industries, where data security is of paramount importance and we ensure that we take the best possible measures to safeguard our customers’ data. With our keenly monitored securities framework, we ensure that our customers’ data is safeguarded and they can continue their business as usual with absolutely no gaps that can lead to the data leak. Here’s a quick overview of the security measures taken at LitmusWorld.
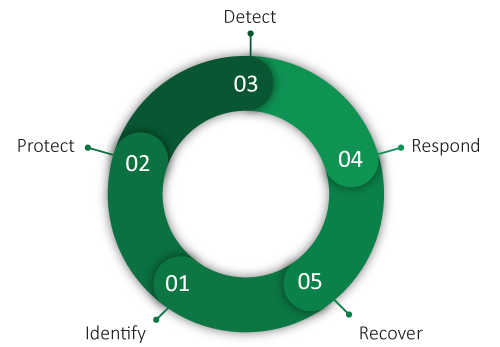
Security Process Chain
- Security Risks are identified at all stages of the operations.
- Threat and Vulnerability assessment ensures that we are protecting all the vulnerable areas with optimum controls.
- Continuous detection of threats are set up with monitoring tools.
- Teams are enabled to respond rapidly to security threats.
- Recovery is met by following the Change management process.

HR Security
HR Security • Employee Entry/Exit Process • Awareness Training and Quizzes • Access Policies & Processes

Physical Security
Physical Security Policy • Access Logs • Review Procedures • Independent Internet Networks • Security Personnel and CCTV Cameras

Email Security
Email Policy • Email Administration Policy • Data Loss Prevention

Business Continuity
BCP Policy • BCP Plan • Restoration Procedure

Change Management
Change Management Policy • Logs Evidence • Exception Management

Incident Management
IM Policy • Incident Reporting • Escalation Matrix • Roles & Responsibilities • Root Cause Analysis
LitmusWorld and GDPR

The European Union’s General Data Protection Regulation (GDPR), which became effective in May 2018, requires companies to become accountable for how they use, manage and maintain the personal data of their customers and employees. Read More ↗.
LitmusWorld is ISO 27001 certified for three consecutive years by a certified ISO agency. Process and Controls are put in place to be GDPR compliant to meet EU data security regulations. Our customers are able to conform to PCI, HIPAA & GLBA or similar laws regulating PII by adapting the options for On-Premise deployment or tokenization – our ability to block PII from appearing on the dashboard outside the IP locked network.

LitmusWorld is now an AWS Qualified Software badge owner after a successful Foundational Technical Review to enhance our enterprise cloud journey. This will help us offer a secure and comprehensive product to our customers to build comprehensive experience management programmes.
